Malvertising on Google Search is an unpleasant occurrence where malicious ads appear in search engine results. These ads are meant to help users find relevant information. But unfortunately, some cybercriminals use paid advertisements to entice users to visit harmful websites and deceive them into downloading malicious software. How does malvertising work? Malvertising is an attack… Continue reading Gozi and IcedID Trojans Spread via Malvertising
Tag: Backdoor
FIN8 Updated Sardonic Backdoor to Deliver Noberus Ransomware
FIN8, an infamous group of cybercriminals, has updated its backdoor malware to avoid being detected. They made improvements and prepared to release a new type of crimeware called Noberus. This threat actor has returned after inactivity, using a modified version of their Sardonic backdoor to distribute the Noberus ransomware. This is a part of their… Continue reading FIN8 Updated Sardonic Backdoor to Deliver Noberus Ransomware
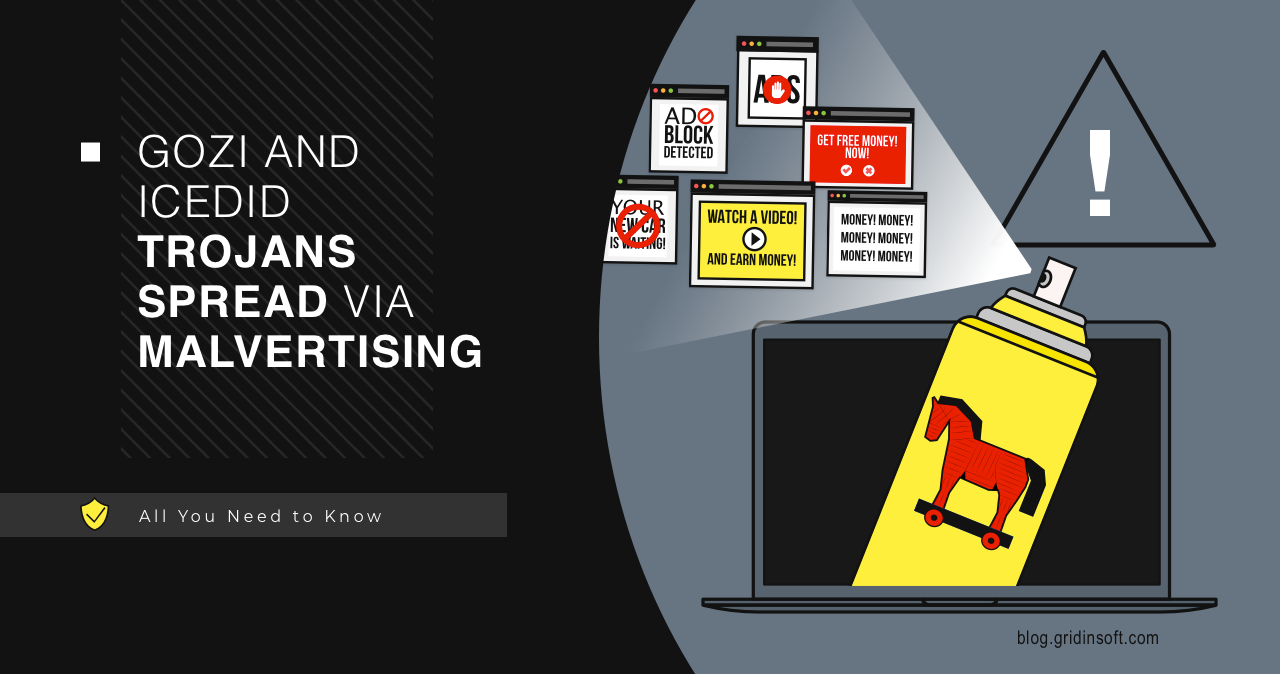
Trojanized TeamViewer Installer Spreads njRAT
Threat actors reportedly started using fake TeamViewer to distribute malware. Their particular favourite for the final payload is the infamous njRAT trojan – an old-timer of the scene. Through the tricky spreading scheme, hackers run a multi-stage attack. njRAT Hides in Trojanized TeamViewer App For some reason, people show high levels of trust towards downloading… Continue reading Trojanized TeamViewer Installer Spreads njRAT
Domino Backdoor is Lead by FIN7 and Conti Actors
A new Domino Backdoor popped out at the beginning of 2023. Since February, a new malware family coined Domino is used for attack on corporations, having Project Nemesis stealer as a final payload. Analysts say that the new backdoor is controlled and developed by ex-TrickBot/Conti actors and hackers related to the FIN7 group. Who are… Continue reading Domino Backdoor is Lead by FIN7 and Conti Actors
IceBreaker Backdoor Emerged, Exploiting New Phishing Way
A new player has appeared in cyberspace, with surprisingly new methods. A previously unknown group attacked gambling and online gaming companies using a yet unknown backdoor, named IceBreaker by researchers. IceBreaker Backdoor exploits new phishing way The method of compromising is based on the fact that tech support workers are tricked into opening malicious screenshots… Continue reading IceBreaker Backdoor Emerged, Exploiting New Phishing Way
Reverse Shell vs. Backdoor : What is the Differences?
Backdoor and Reverse Shell are very similar, which may lead you to believe they are the same thing. But take your time with conclusions on this point; we have given you the below guidance on the difference between the two mechanisms. What is Backdoor? Backdoors are methods of bypassing a computer’s security measures that aren’t… Continue reading Reverse Shell vs. Backdoor : What is the Differences?
Signs of Identity Theft: How to Prevent It?
Identity theft is a rather unpleasant crime. Cybercriminals can not only empty your wallet but also stalk your digital space and may even use it to commit crimes on your behalf. Since criminals invent new tricks daily, keeping yourself safe is pretty hard. So we’ve set together some essential tips to help prevent identity theft… Continue reading Signs of Identity Theft: How to Prevent It?
CloudMensis Malware Attacks MacOS Users
ESET experts have discovered the CloudMensis malware, which is used to create backdoors on devices running macOS and subsequently steal information. The malware received its name due to the fact that it uses pCloud, Dropbox and Yandex.Disk cloud storages as control servers. Let me remind you that we also wrote that Vulnerability in macOS Leads… Continue reading CloudMensis Malware Attacks MacOS Users
SYMBIOTE Backdoor and Rootkit Dropper Revealed
Symbiote Backdoor: a Stealthy and Highly Evasive Linux Malware Researchers at Blackberry and Intezer have revealed a malignant program dubbed Symbiote used to inject rootkits and backdoors into compromised Linux servers. This software has been targeting financial institutions throughout South America. To install the pest into the system, the malefactors need root access, which they… Continue reading SYMBIOTE Backdoor and Rootkit Dropper Revealed
Chinese Hacker Group Revealed after a Decade of Undetected Espionage
The New Chinese Spying Threat Actor Identified SentinelLabs, an American cybersecurity company, has reported about a Chinese hacking group Aoqin Dragon, which has managed to conduct successful spying activities against companies in Australia and South Asia for about ten years without being tracked. Different cybersecurity companies partially encountered the group’s actions in the past, but… Continue reading Chinese Hacker Group Revealed after a Decade of Undetected Espionage




![Signs of Identity Theft: How to Prevent Identity Theft [Short Guide 2022 ]](https://gridinsoft.com/blogs/wp-content/uploads/2022/09/istockphoto-1279316333-612x612-1.jpg)