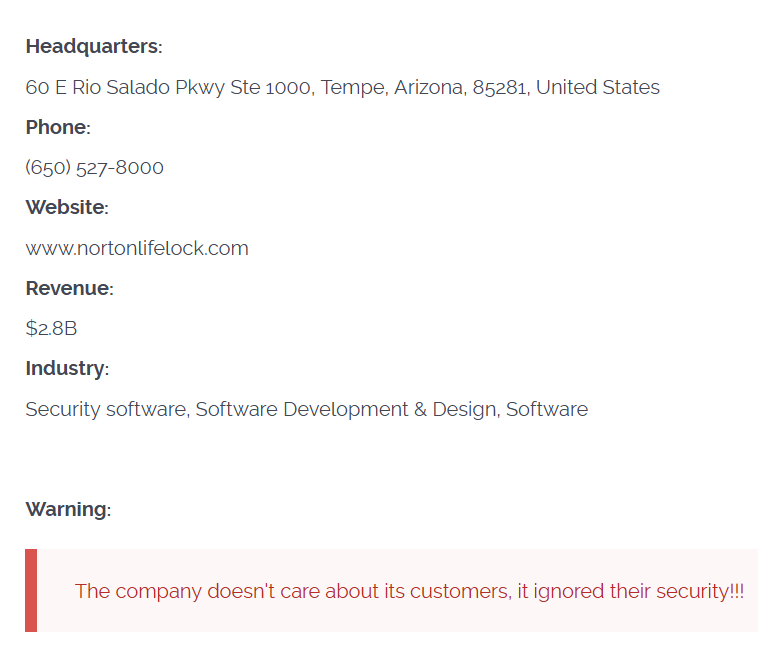
NortonLifeLock, the world-famous antivirus software developer, had reportedly been hacked by the Cl0p ransomware gang. Hackers listed it on their Darknet leak page, and it appears that the cybersecurity vendor is yet another victim of MOVEit vulnerability.
NortonLifeLock Hacked via MOVEit Vulnerability
The vulnerability in Progress’ MOVEit MFT solution set the whole cybersecurity community abuzz. It allowed hackers to send external login requests to the cloud SQL database. After a successful brute force in such a manner, the crooks were receiving full access to the web repository – meaning they could upload their files and manage existing ones. Despite the patch being released pretty soon after the vulnerability discovery, it was too late. Threat actors, particularly ones who stand behind Cl0p ransomware, successfully abused the vulnerability to breach into the companys’ networks.
NortonLifeLock company, the developer of a famous Norton Antivirus, appears to be hacked via this breach as well. Along with 80+ other companies, it was listed on the Cl0p’s Darknet leak site since the beginning of summer 2023. It is not clear though whether exactly MOVEit vulnerability was used, and if it was – which one of several uncovered ones was used.
What is Cl0p Ransomware?
Cl0p ransomware gang is a Russian ransomware project backed by the threat actor known under the FIN7/Sangria Tempest name. A lot of facts point at FIN7 being related to Russian external reconnaissance service (a.k.a. SVR). The gang is famous for its cheeky pick of targets, particular passion at hacking into educational institutions and heavy use of novice software vulnerabilities. Earlier this year, Cl0p ransomware was spread after the use of vulnerability in PaperCut – another MFT solution. Though, the list of all security breaches it uses is obviously far bigger.
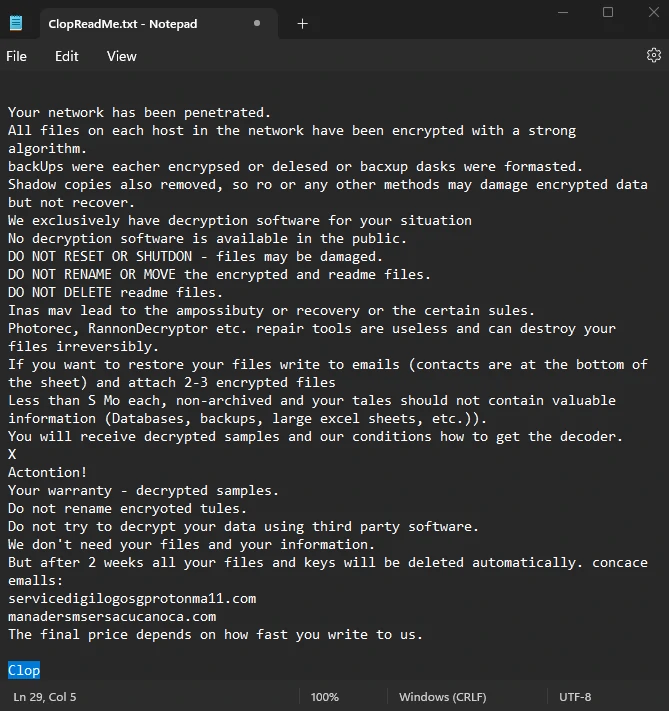
Getting back to the Norton hack, in the note on the Darknet site, Cl0p said nothing about the negotiations. If the company refuses to pay, hackers disclose this fact and publish the leaked data. This is not the case of Norton – their record says only about the fact of the hack. The negotiation commonly takes up to several weeks – especially if the company is ready to pay, but wishes to discuss the ransom sum.
How to protect against MOVEit vulnerability?
For any cybersecurity company, being hacked is a big reputational loss. Even though Norton is not guilty of MOVEit vulnerabilities, they were hacked and potentially let the user information leak – and that is already image-busing. Though until the detailed info regarding how exactly it was hacked, and how much data is lost, it is hard to say whether the users suffer or not. And despite Norton being not entirely guilty in this situation, they could use several preventive measures that minimise the chances of zero-day vulnerability exploitation.
Probably, the best method for 0-day counteraction is using a zero-trust security solution. They have their disadvantages – particularly high resource consumption and higher access delays – but their effectiveness is exceptionally good. When set up properly, they will not allow any program to perform an action without the diligent checkup, and that is what could have stopped the Cl0p at the moment of MOVEit breach exploitation.



My computer appears to have been hacked during 15th Sept. 2023 when I was actually accessing the Norton software to make a complaint. I exited the program and turned the computer off. For the next week from 16th Sept I could not make any contact with Norton by chat, email, phone etc. – I was shut out and many of my computer files were corrupted or vanished. Normal service was was restored by 23rd Sept but only when Norton started reminding me that my next annual subscription was due. I cannot find anything on the net which confirms that Norton itself was hacked. I have not heard from Norton itself and I have now closed my Norton Account because I cannot trust them any more.