Trojan:Script/Phonzy.B!ml is a generic detection name used by Microsoft Defender. This type of malware is categorized as a loader as it mainly aims at delivering malicious payloads onto infected systems. Throughout hundreds of infection cases, Phonzy trojan was noticed to often deliver banking trojans.
Trojan:Script/Phonzy.B!ml Overview
Trojan:Script/Phonzy.B!ml is a generic detection name that Windows Defender uses to mark small malware families. Such malicious programs may have similar behavior and code elements but belong to different groups.
For functionality, Phonzy.B!ml is a scripted dropper malware. Its main purpose is to download and launch the additional malware in a manner that does not require user interaction. However, Phonzy samples are able to collect some basic information regarding the system, like location, OS version, and things the like. A typical payload delivered in Phonzy malware attacks is banking trojans – a specific type of stealers, which aims precisely at online banking information.
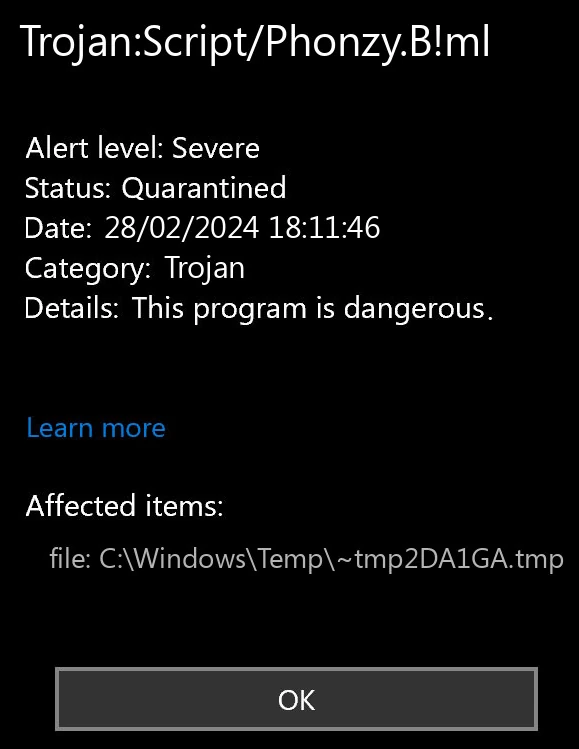
Is Phonzy B!ml False Positive?
The deeper look at the naming convention Microsoft uses in its detection names shows that the “!ml” particle stands for “machine learning”, meaning their AI detection engine has detected the file. Despite being highly effective and promising, it requires the confirmation of a signature detection system. Without this confirmation, it is particularly easy to get a lot of false positive detections.
Unfortunately, there is barely a way to distinguish between real and false detections. Modern malware does its best in hiding among legitimate programs and files, so file locations are not informative. That is the reason why I recommend scanning your system with GridinSoft Anti-Malware.
Phonzy.B!ml Technical Analysis
Since Phonzy is a generic detection name, it is rather hard to find a well-known sample to analyze. For that reason, I’ve done a comprehensive analysis of several ones – to have a better understanding of what this malware is capable of. In short – a rather simple dropper that can make a huge mess in the system it infects.
Launch & Unpacking
The majority of Phonzy samples that I’ve encountered arrive in a packed form – encrypted and/or archived. This is usually done for 2 reasons – to avoid the static detection and complicate the analysis. In the case of Phonzy, I’m leaning toward the first option.
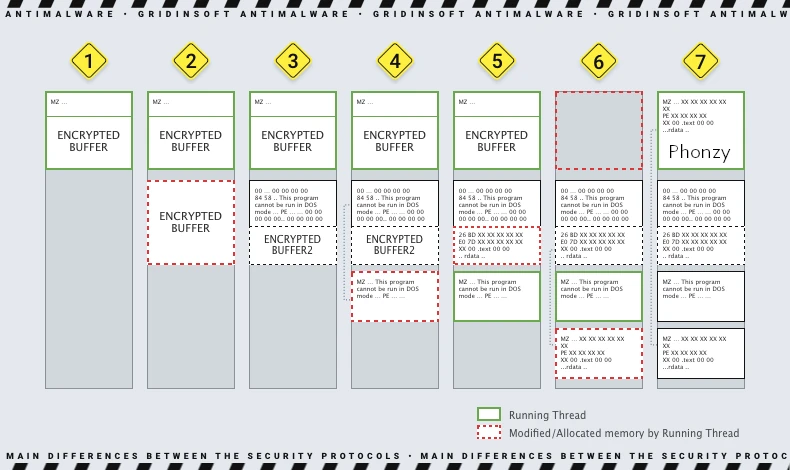
To perform the unpacking, Phonzy relies on the script that downloads it to the system. Usually, this is a PowerShell script that pulls the dropper from the intermediary server, and it is also responsible for launching one. A part of it is responsible for unpacking and launching the sample after downloading.
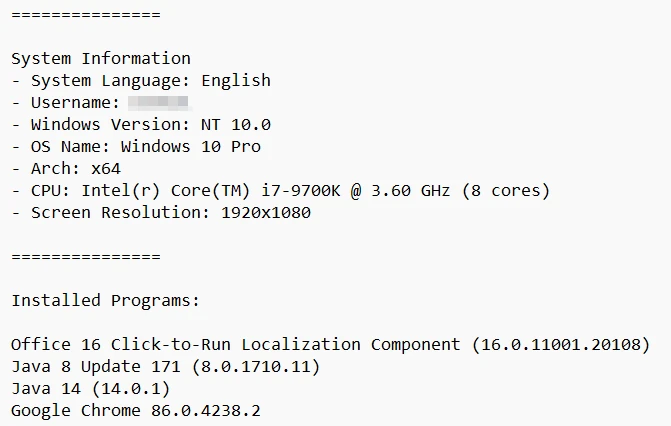
Gathering system information
Once launched, Trojan:Script/Phonzy.B!ml collects basic information about the target system. This may include the operating system version, hardware information, a list of installed programs and devices, and the device’s geolocation. Such information is mostly needed to fingerprint the system, i.e. give it a specific name corresponding to its internals. In addition to system info, some of the Phonzy.B!ml samples were able to take screenshots of the infected device’s screen.
Contacting Command & Control Server
The next step in the attack is contacting the command server. Malware sends an HTTP POST request to the C2, to notify about a new infection and send the collected data. Depending on the server response, malware may switch to idle or start downloading other malware. Overall, the C2 communications for Phonzy are simple and insignificant.
Delivering other malware
The key action of Phonzy Trojan is, obviously, deploying other malware samples to the infected system. It receives the instructions from the C2 in a form of IP address it should pull the payload from, and the way this payload should be launched. Usually, the said IP address corresponds to a compromised website that hackers use as an intermediary server.
For the ways to run the payload, the options are quite typical for droppers. All of the Phonzy samples I’ve analyzed were able to work with DLLs and executable files. The former can be launched through DLL hijacking and a hookup to the system DLL, while the latter is about the regular .exe run.
Self-Propagation to USB Drives
Some of the inspected variants are Phonzy.B!ml were capable of self-propagating via attached flash drives or other removable storage media. This is a rather unusual trick for modern malware, as security vendors elaborated the ways to detect virus-like spreading long ago. Nonetheless, you cannot deny effectiveness – a single infected USB drive is capable of infecting dozens of other systems without even a single click from malware masters.
How To Remove Trojan:Script/Phonzy.B!ml
To remove Phonzy B!ml, I’d recommend using GridinSoft Anti-Malware. The fact that dropper malware can spread a lot of other malware requires using advanced software to remove it all. GridinSoft Anti-Malware will check every little bit of the system and eliminate even the stealthiest malware.

Download and install Anti-Malware by clicking the button below. After the installation, run a Full scan: this will check all the volumes present in the system, including hidden folders and system files. Scanning will take around 15 minutes.
After the scan, you will see the list of detected malicious and unwanted elements. It is possible to adjust the actions that the antimalware program does to each element: click "Advanced mode" and see the options in the drop-down menus. You can also see extended information about each detection - malware type, effects and potential source of infection.
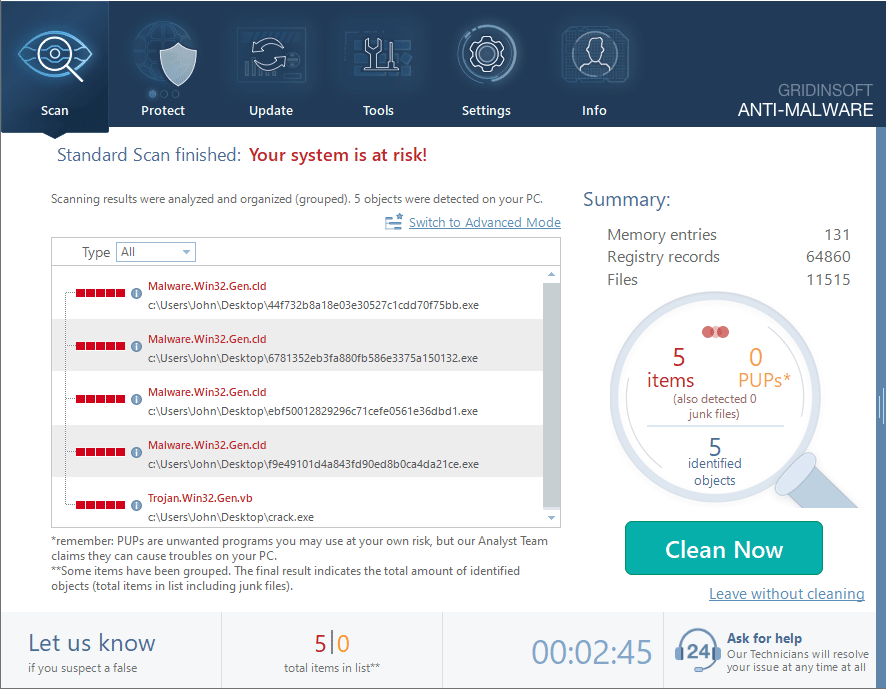
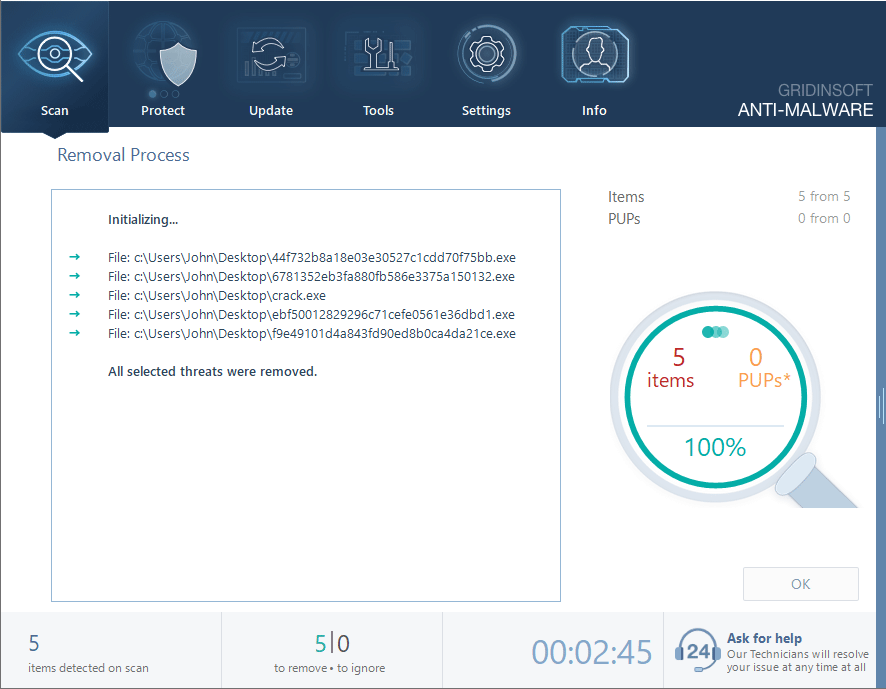
Click "Clean Now" to start the removal process. Important: removal process may take several minutes when there are a lot of detections. Do not interrupt this process, and you will get your system as clean as new.
Safety Recommendations
To avoid infection of your system, it is sufficient to follow basic cyber hygiene. The first rule is to avoid pirated software and sites that distribute it. Cracked software is an ideal shell for malware delivery, so it is not just about being careful – it is about staying away.
Having an advanced protection tool, like Gridinsoft Anti-Malware, is another key to make your system secure. Proactive protection coupled with an AI detection engine will weed out all the attempts of malicious software to get in. Also, its Removable Device Protection feature will block the Phonzy trojan attempting to infect the system via an USB drive.