Mobile Security
Microsoft warns of dangerous vulnerability in Surface Pro 3 devices
Microsoft engineers have published a security bulletin on a new vulnerability affecting Surface Pro 3 tablets. The bug could be…
Ukrainian cyber police arrested ransomware operators who “earned” $150 million
Ukrainian Cyber Police have arrested two operators of an unnamed ransomware. It is reported that the operation was carried out…
Experts showed fraudulent payments from a locked iPhone with Apple Pay and a Visa card
Scientists talked about how to make fraudulent payments using Apple Pay with a Visa card on a locked iPhone. This…
Encryption algorithms for 2G networks have been intentionally weakened
A group of scientists from several European universities published a report on encryption algorithms for 2G networks, which many information…
Google stopped trying to shorten URLs in the address bar
Google’s experiment with attempt to shorten URLs (hiding parts of the URL from the address bar) has finally failed and…
Microsoft urges users to opt out of multi-factor authentication via phone
Microsoft experts have once again raised the issue of the…
Platypus attack allows stealing data from Intel processors
A group of scientists from the Technical University of Graz…
Experts discovered that many mobile browsers are vulnerable to url spoofing
Rapid7 analysts and independent information security expert Rafay Baloch discovered…
MalLocker ransomware easily tricks Russians, pretending to be a screen lock from the police
Microsoft experts talked about the new Android ransomware AndroidOS/MalLocker. (hereinafter…
Cellmate men’s chastity belts are vulnerable to attacks and dangerous for users
Pen Test Partners analysts have studied an extremely unusual device:…
Google recruits a team of experts to find bugs in Android applications
ZDNet reports that a number of new positions have been…
Attackers can bypass TikTok multi-factor authentication through the site
Journalists of the ZDNet publication, citing one of their readers,…
Microsoft left open one of the internal servers of the search engine Bing
Ata Hakcil, cyber security specialist at WizCase, discovered that Microsoft…
SpiKey technique allows opening the lock by recording a sound of a turning key
Scientists from the National University of Singapore have published a…
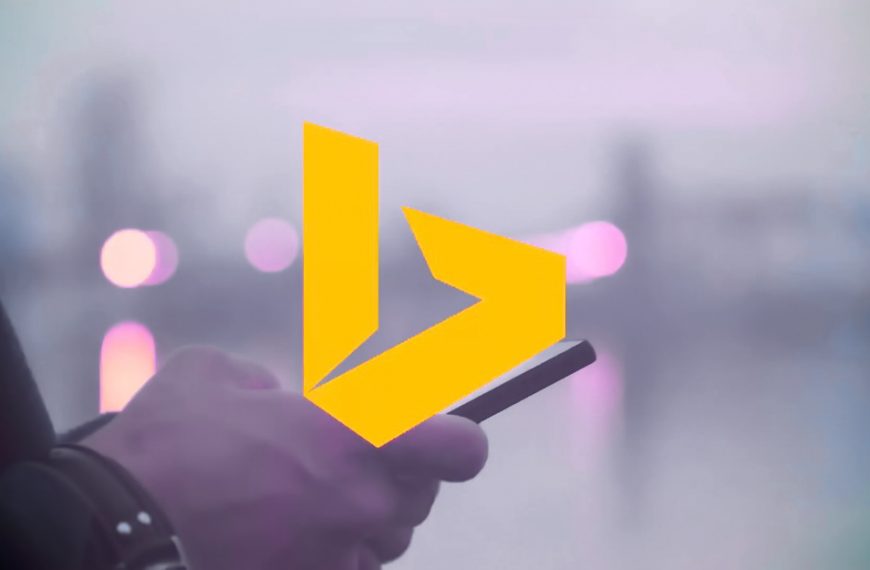
ReVoLTE attack allows overhearing other people’s conversations in LTE networks
Experts from the Ruhr University and New York University in…
Citrix expects attacks on fresh issues in XenMobile
Citrix engineers released a number of Citrix Endpoint Management patches…
Media Reports that Garmin Paid Ransom to WastedLocker Malware Operators
In July 2020, Garmin, the manufacturer of wearable electronics and…