The spam texts can include spam emails and spam calls. These are all unwanted and often annoying text messages whose sender you don’t know. The purpose of such spam is to deceive the user and get his confidential information or draw you into the phishing attempt. These statements are received from a computer programmed to… Continue reading How to Stop Spam Texts?
Tag: iPhone
Scam Likely Calls: How to block them?
Have you ever glanced at your phone and seen the caller ID flash “Scam Likely”? Understanding what this alert means, why it appears, and how you can stop these calls is essential for protecting yourself from potential fraud. Here’s everything you need to know about the “Scam Likely” feature. What Does “Scam Likely” Mean? For… Continue reading Scam Likely Calls: How to block them?
ChatGPT Causes New Wave of Fleeceware
Artificial intelligence is one of the most significant advances in technology. It is used in one way or another everywhere, from voice input recognition on your smartphone to autopilot systems in cars. But the latest development in the industry – the launch of OpenAI’s ChatGPT, which has caused a stir even to the point that… Continue reading ChatGPT Causes New Wave of Fleeceware
Was Your Apple ID Hacked? Here’s How To Secure Your Account
Apple’s services and products are only accessible through their walled garden. Users can only access the company’s products and services with an Apple ID. If someone figures out your Apple ID credentials, there’s a lot of personal data at risk. Anyone with access to the account can read all emails, regardless of whether they are… Continue reading Was Your Apple ID Hacked? Here’s How To Secure Your Account
Calendar Virus Removal on iPhones & Mac
Calendar virus may not sound familiar to most users. What’s likely happening is that a calendar is spamming you with appointments; it’s just mistakenly appeared in your calendar. Whenever you receive a notification from one of these appointments, you must refrain from clicking any links within the message. Doing so could infect your device with… Continue reading Calendar Virus Removal on iPhones & Mac
Spy method NoReboot allows simulating iPhone shutdown and prying through the camera
The NoReboot spy method allows intercepting the iPhone restart and shutdown process and prevent them from ever happening. ZecOps has developed a new method to simulate restarting or shutting down the iPhone and thereby prevent the removal of malware from it, with which hackers can secretly track the victim through the microphone and phone camera.… Continue reading Spy method NoReboot allows simulating iPhone shutdown and prying through the camera
Vulnerability in Apple iCloud puts billion users at risk
Security of over a billion iPhone owners and users of popular instant messengers is at risk due to a vulnerability in Apple iCloud. As the Forbes reports, private messages sent via iMessage and WhatsApp on iPhone are not secure when using factory settings. While encrypted apps like iMessage and WhatsApp keep messages on the device… Continue reading Vulnerability in Apple iCloud puts billion users at risk
Experts showed fraudulent payments from a locked iPhone with Apple Pay and a Visa card
Scientists talked about how to make fraudulent payments using Apple Pay with a Visa card on a locked iPhone. This scam works over the air, even if the iPhone is in your bag or pocket, and has no limit on the number of transactions. A report on this issue [PDF] will be presented at the… Continue reading Experts showed fraudulent payments from a locked iPhone with Apple Pay and a Visa card
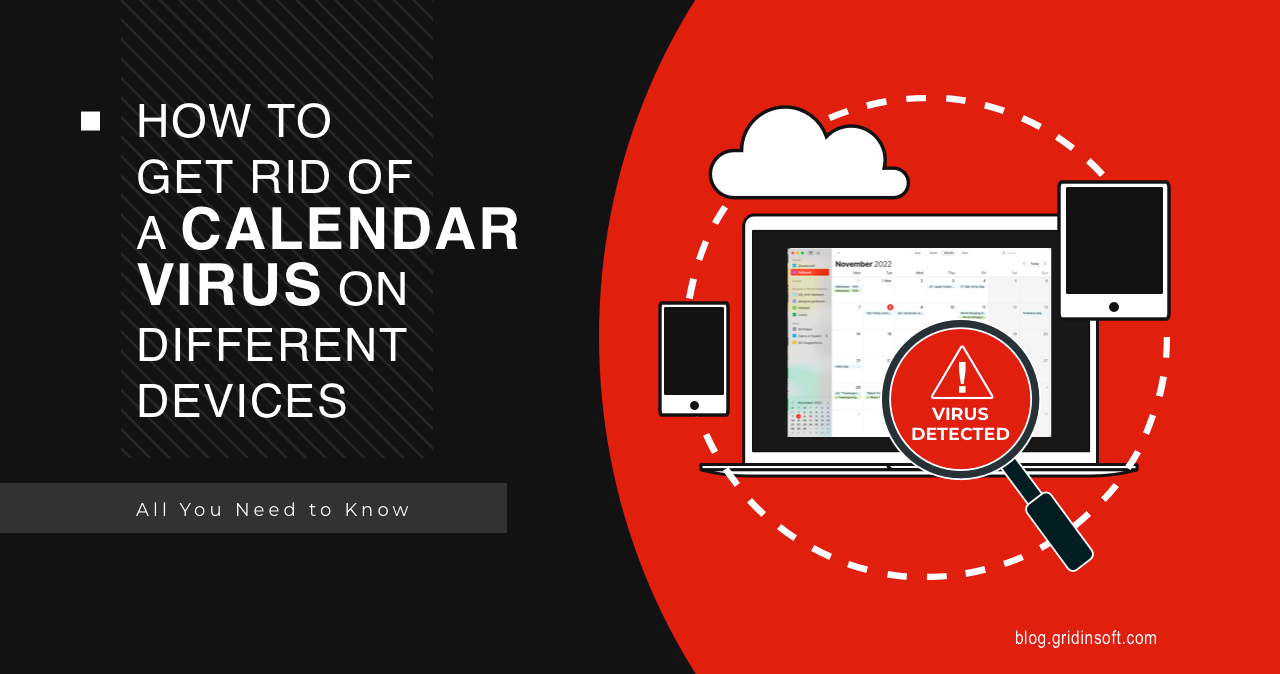
Cybersecurity expert created an exploit to hack iPhone via Wi-Fi
Google Project Zero expert Ian Beer has demonstrated an exploit to hack iPhone and other iOS devices remotely and without user interaction. The underlying critical vulnerability CVE-2020-3843, discovered by the researcher, made it possible to remotely steal sensitive data from any device in the Wi-Fi hotspot without any user’s interaction. The exploit, which Bier worked… Continue reading Cybersecurity expert created an exploit to hack iPhone via Wi-Fi
Kr00k problem threatens devices with Qualcomm and MediaTek Wi-Fi chips
In early 2020, ESET experts spoke about the Kr00k vulnerability (CVE-2019-15126), which can be used to intercept and decrypt Wi-Fi (WPA2) traffic. Then it was reported that any devices using the solutions of Cypress Semiconductor and Broadcom, from laptops and smartphones to routers and IoT devices, are susceptible to this problem. Now there is information… Continue reading Kr00k problem threatens devices with Qualcomm and MediaTek Wi-Fi chips